Rep tells T-Mobile subscriber that SIM swap attack on his account was an "inside job"

In case you're not familiar with what a SIM swap is, it is a way for thieves to take control of your phone by obtaining a SIM card meant for your device and inserting it into their own phone. Once this is done, the thief makes changes to various passwords and credentials locking you out of your own device. The attacker gets free access to your financial apps, wires your money to their own accounts, and wipes you out. You might think that you're protected because you have two-factor authorization (2FA) which sends a code that must be correctly applied before an app is opened, but you're not.
Once the attacker inserts your SIM in his device, any 2FA notifications will go to him allowing the criminal to type in the correct code. This verifies your identity as far as a financial institution is concerned even though it is not you controlling the activity taking place on your phone.
How does a thief obtain a SIM card that gives them control of your phone?
So how does a bad actor get your SIM card? Well, one way is for him to walk into one of a carrier's retail stores and pretend to be you asking for a new SIM card. Hopefully, most reps will ask for ID first, but we've heard about some situations where there was no request to see a photo ID. Another scarier method involves a paid-off rep who hands over a new SIM card to someone pretending to be you because, well, he was paid well to do so.
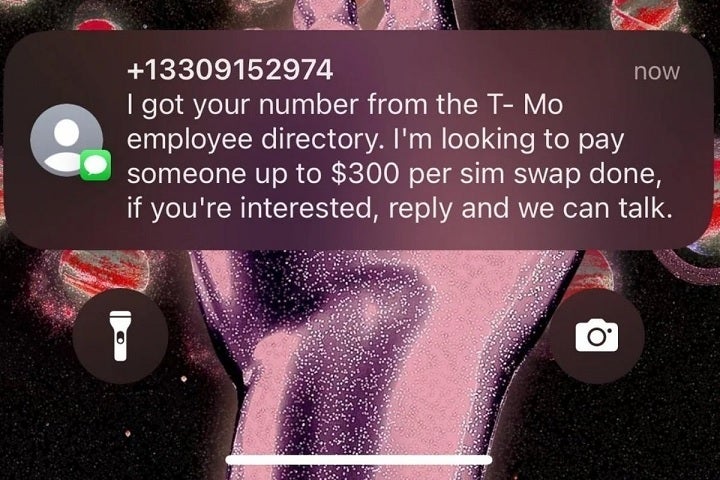
Earlier this year some T-Mobile reps received texts trying to get them to help pull off SIM swaps against T-Mobile customers.
Do you think that sounds paranoid? Not only have employees of wireless firms been caught in such a scheme, you might recall that last April several T-Mobile employees reported receiving text messages from someone offering them $300 for each successful SIM swap they help pull off.
Today, a T-Mobile subscriber said that one of the lines in his account was twice the victim of a SIM swap. The line belongs to his brother who is a ride-share driver and needs his phone line for his job. The first time it happened, the brother went to the store and had the SIM swap switched back which was a stroke of luck. The brother had no idea what a SIM swap attack was at the time. The second time it happened, the owner of the account was overseas but he still managed to call T-Mobile. That call was billed at international rates although the carrier did reverse that charge eventually).
"Later on I called and asked for a supervisor and demanded the investigation and results to be made available to me. (The day incident happened, the rep told me it was taking place from a store by a store rep) so clearly it was an insider act. The supervisor said they can’t disclose any disciplinary action due to security and privacy reasons, I was like clearly you don’t give a fxxk about my security and privacy." @jaylin0130
The T-Mobile rep that the account owner was speaking to while overseas informed him that it was an "inside job" and that a store rep was responsible for the actions that led his brother to be the victim of a SIM swap. Even though this took place last year, the owner of the account only recently received a letter from T-Mobile confirming that a SIM number assigned to his account was changed without approval.
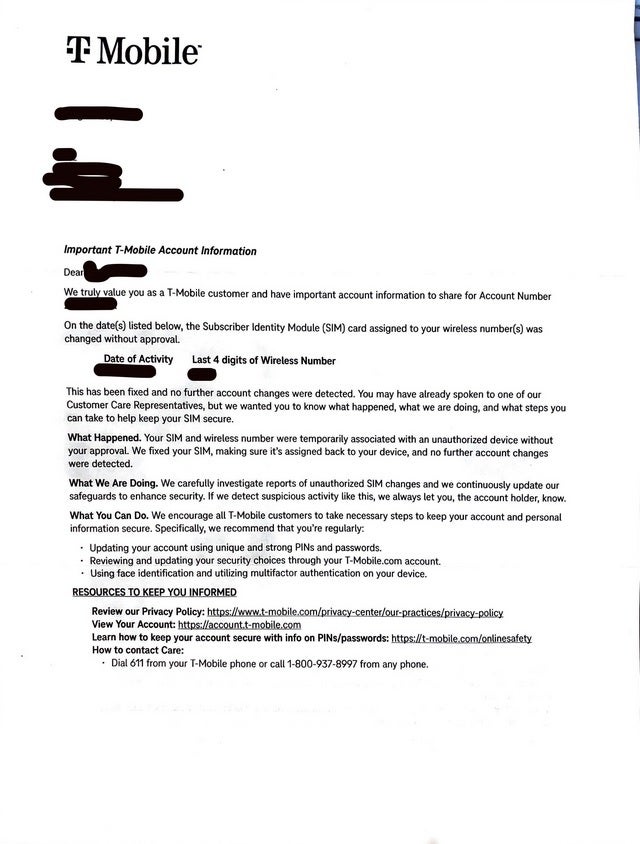
T-Mobile acknowledges that one of its customers was the victim of a SIM swap attack. | Image credit-@jaylin0130
The letter from T-Mobile said that the customer's SIM and wireless number "were temporarily associated with an unauthorized device" without the account owner's approval. The carrier goes on to say in the letter that it fixed the SIM making sure that it was assigned back to the proper device.
T-Mobile has some suggestions to strengthen your protection against SIM swaps
Considering that T-Mobile told the owner of the account that an insider was involved in the SIM swap, this should be a warning to every single person using a cellular phone to take quick action if they receive a notification that their SIM card is no longer connected to their account number. Another way to detect a possible SIM swap in action is the inability to make or take a phone call or send or receive a text message on your device. If this happens to you, without delay get to a working phone, call your carrier, and tell them that your the victim of a SIM swap.
To better protect your account, T-Mobile suggests that you update your account using unique and strong PINs and passwords. You should also use the T-Mobile.com page to review and strengthen your security options. You should also use facial recognition and multi-factor authentication on your device although the latter might not be of any help once a SIM swap attack has been in force.
T-Mobile now offers a SIM Protection feature
To show you how lacking security is when it comes to SIM cards in the wireless industry, during the first attack on the brother's phone line, he was able to get a new SIM card even though he was not an authorized user of the account. Be alert!
T-Mobile now has a SIM Protection feature that requires you to disable the feature before moving a SIM or eSIM to a new device. If the feature is not disabled, the SIM swap will not work. This will not work on eSIMs used with iPhone models. T-Mobile postpaid subscribers need to log in to the T-Mobile app or T-Mobile.com with their T-Mobile ID. While you can add SIM Protection as an Authorized User, only the Primary Account Holder can remove the feature.
To add this feature to T-Mobile Prepaid accounts, log in to T-Mobile.com with the primary line's T-Mobile ID.
Follow us on Google News












Things that are NOT allowed:
To help keep our community safe and free from spam, we apply temporary limits to newly created accounts: